BQT Sideload Locks: Superior Safety Solutions for Modern Needs
Wiki Article
The Future of Safety: Discovering the current Patterns in Electronic Safety And Security Technologies
In the world of security and safety, the landscape is constantly advancing, driven by technical developments that push the limits of what is possible. Digital security technologies have actually come to be increasingly innovative, offering cutting-edge options to attend to the ever-growing obstacles faced by people and organizations alike. From biometric verification to the integration of synthetic intelligence and machine learning, these patterns hold the guarantee of enhancing protection actions in unprecedented means. As we browse via this complex internet of developments, one can not assist yet ask yourself just how these modern technologies will form the future of safety and protection, establishing the phase for a brand-new era of security and durability (BQT Locks).Rise of Biometric Authentication
With the increasing need for secure and practical verification techniques, the increase of biometric verification has actually transformed the way people access and protect their sensitive information. Biometric verification uses one-of-a-kind organic characteristics such as finger prints, face functions, iris patterns, voice acknowledgment, and also behavior attributes for identity verification. This technology offers an extra trustworthy and safe technique compared to standard passwords or PINs, as biometric information is incredibly tough to duplicate or swipe.One of the crucial benefits of biometric authentication is its convenience. Users no more need to keep in mind complex passwords or stress over losing access due to neglected credentials. By just using a part of their body for confirmation, individuals can swiftly and safely accessibility their devices, accounts, or physical spaces.
Furthermore, biometric verification boosts security by offering a more robust protection against unauthorized gain access to. With biometric markers being one-of-a-kind to every individual, the danger of identity burglary or unauthorized entrance is dramatically lowered. This enhanced degree of safety and security is particularly vital in markets such as finance, health care, and government where protecting delicate information is extremely important.
Combination of AI and Machine Understanding
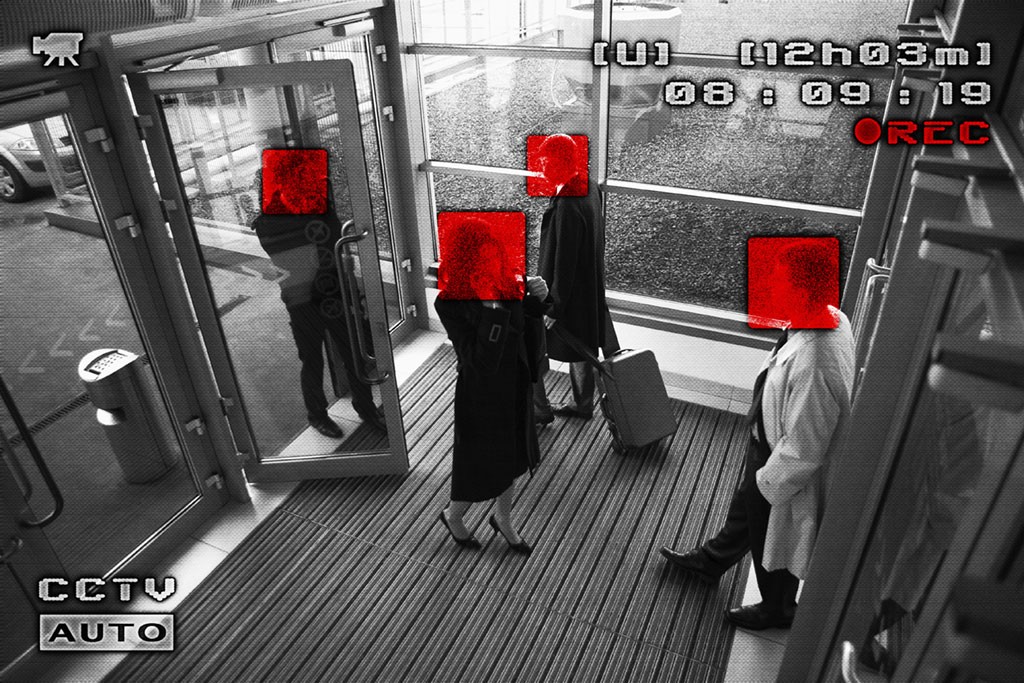
The advancement of electronic safety and security technologies, exemplified by the increase of biometric verification, has led the way for advancements in the integration of AI and Maker Knowing for enhanced identification and protection mechanisms. By leveraging AI formulas and Maker Discovering models, digital safety systems can now examine vast quantities of information to identify patterns, anomalies, and possible threats in real-time. These technologies can adapt to progressing security threats and provide positive responses to mitigate threats properly.One considerable application of AI and Maker Knowing in digital protection is in anticipating analytics, where historical data is made use of to forecast possible security breaches or cyber-attacks. This proactive method permits protection systems to prepare for and protect against threats before they occur, boosting overall safety procedures. In addition, AI-powered surveillance systems can intelligently check and assess video clip feeds to determine questionable activities or individuals, boosting action times and reducing false alarms.
IoT and Smart Protection Tools
Improvements in digital safety and security modern technologies have brought about the development of IoT and Smart Protection Devices, changing the method safety systems operate. The Web of Things (IoT) has actually made it possible for protection devices to be adjoined and from another location easily accessible, offering enhanced monitoring and control capacities. Smart Safety Devices, such as smart cameras, door locks, and movement sensing units, are geared up with performances like real-time alerts, two-way communication, and assimilation with other wise home systems.One of the considerable advantages of IoT and Smart Safety Tools is the capability to supply individuals with smooth access to their security systems via mobile phones or various other internet-connected devices. This benefit enables remote monitoring, equipping, and deactivating of safety and security systems from anywhere, providing property owners with assurance and flexibility. These gadgets commonly include advanced attributes like facial acknowledgment, geofencing, and task pattern acknowledgment to improve total safety levels.
As IoT remains to advance, the combination of expert system and artificial intelligence algorithms right into Smart Protection Gadgets is expected to further enhance detection accuracy and modification alternatives, making digital safety systems even extra efficient and reliable.
Cloud-Based Safety Solutions
Arising as an essential facet of modern electronic safety framework, Cloud-Based Safety and security Solutions supply unmatched flexibility and scalability in protecting electronic assets. Cloud-based safety services enable remote tracking, real-time alerts, and centralized management of security systems from any kind of place with a net connection.Furthermore, cloud-based safety solutions use automated software program updates and upkeep, making certain that security systems are always current with the newest securities against arising dangers. Overall, cloud-based safety and security solutions represent an economical and efficient means for businesses to boost their safety posture and safeguard their digital possessions.
Focus on Cybersecurity Steps
With the enhancing sophistication of cyber dangers, services are positioning a paramount concentrate on bolstering their cybersecurity steps. BQT Locks. As innovation breakthroughs, so do the approaches utilized by cybercriminals to breach systems and steal delicate details. This has actually triggered organizations to spend heavily in cybersecurity measures to shield their information, networks, and systems from harmful assaults
One of the crucial fads in cybersecurity is the fostering of innovative file encryption protocols to protect information both at remainder and in transportation. Security helps to make sure that also if information is intercepted, it continues BQT Biometrics Australia to be unreadable and secure. In addition, the application of multi-factor verification has become progressively common to add an additional layer of safety and security and validate the identifications of individuals accessing sensitive information.

Final Thought
Report this wiki page